The German Cyber Criminal Überfall: Shifts in Europe's Data Leak Landscape

- AI驱动的自动化本地化正打破语言壁垒,使非英语国家成为勒索软件新目标。
- 英美大企业安全加固与保险理赔促使攻击者转向防御相对薄弱的德国中型企业。
- 头部勒索团伙受打击后生态碎片化,中端组织涌入加剧竞争,公开泄露数据激增部分源于谈判策略转变。
Written by: Jamie Collier, Robin Grunewald
- * *
Germany has reclaimed its position as a primary focus for cyber extortion in Europe. While data leak site (DLS) posts rose almost 50% globally in 2025, Google Threat Intelligence (GTI) data shows that the surge is hitting German infrastructure harder and faster than its regional neighbors, marking a significant return to the high-pressure levels previously observed in the country during 2022 and 2023.
Cyber Criminals Pivoting Back to Germany
Germany moved to the forefront of European data leak targets in 2025. Following a 2024 period where the UK led in DLS victims, this pivot reflects a resurgence of the intense pressure observed across German infrastructure during 2022 and 2023.
This targeting is not a result of the overall number of companies within Europe, as Germany has fewer active enterprises than France or Italy. Instead, its sustained appeal to extortion groups is driven by its status as an advanced European economy with an increasingly digitized industrial base.

Figure 1: Percentage of data leaks affecting European nations in 2025
The speed of this escalation is particularly notable. Following a relative cooling of activity in 2024, Germany saw a 92% growth in leaks in 2025—a growth rate that tripled the European average.

Figure 2: The number of German victims listed in data leak sites grew 92% in 2025 compared to 2024
While several factors influenced European ransomware trends in 2025, a striking contrast emerged in leak volumes. While shaming-site postings for UK-based organizations cooled, non-English speaking nations (particularly Germany) witnessed a surge. This shift reflects a convergence of several factors. The continued maturation of the cyber criminal ecosystem, including the use of AI to automate high-quality localization, is further eroding the historical protection offered by language barriers. However, this "linguistic pivot" is also supported by a shift in victim profiles. As larger "big game" targets in North America and the UK improve their security posture or utilize cyber insurance to resolve incidents privately, threat actors appear to be pivoting toward the "ripe markets" of the German Mittelstand (discussed in further detail later in this post).
Google Threat Intelligence Group (GTIG) has also observed multiple cyber criminal groups post advertisements, seeking access to German companies and offering a proportion of any extortion fees obtained from victims. For example, dating back to November 2024, the threat actor known as Sarcoma has targeted businesses across several highly developed nations, including Germany.
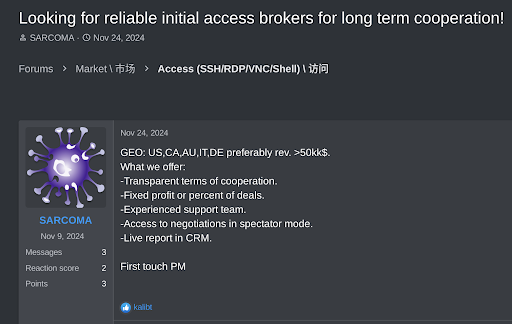
Figure 3: A forum post by an actor seeking a partnership to target German victims
While the 2025 data marks a record year for German leak volume, it is important to contextualize these figures with a degree of caution. Relying solely on DLS numbers can be misleading, as threat actors typically only post victims who refuse to initiate or complete extortion negotiations. Public reporting on the decline in ransom payment rates may be partially fueling the steady increase in shaming site posts as a secondary pressure tactic. Consequently, while the surge in Germany remains a critical trend, these metrics should be viewed as one component of a broader, more complex threat landscape.
The Diversifizierung of the Cyber Criminal Ecosystem
2025 was characterized by significant turbulence in the cyber criminal ecosystem, driven by internal conflicts and aggressive law enforcement actions against dominant "big game" operations like LOCKBIT and ALPHV. The resulting vacuum at the top of the ransomware market has led to a more crowded field of agile, mid-tier DLS brands. In Germany, this rebalancing is highly visible: as established brands receded, a wider pool of competitors emerged to absorb the market share.

Figure 4: German victims on data leak sites rose sharply in 2025
Following the disruption of LockBit, groups such as SAFEPAY and Qilin have gained significant prominence within the German landscape. SAFEPAY, in particular, claimed breaches of 76 German companies in 2025—accounting for 25% of all German victim posts that year. Meanwhile, Qilin tripled its operational tempo in Germany during Q3 2025. While this increase aligns with Qilin's broader global uptick in activity, their consistent focus on German targets (including 13 victims posted already in early 2026) demonstrates that their presence in the German landscape grows in lockstep with their global expansion.

Figure 5: Leaked data of a German company (name redacted) by SafePay
No Such Thing as Too Small: Targeting of the Mittelstand
There is a persistent myth that small businesses are "too small" to be targeted, a perception often fueled by the fact that large global corporations often dominate cyber crime headlines. However, the 2025 data tells a different story: organizations with fewer than 5,000 employees accounted for 96% of all ransomware leaks in Germany. While this figure largely aligns with the structural composition of the German economy, it underscores a concerning disconnect between public perception and actual targeting patterns. While "big game" hits make the news, the high volume of leaks among medium- and small-sized victims proves they are highly attractive targets for cyber criminals—often because they lack the extensive security personnel and specialized resources of their larger counterparts.
The targeting of the Mittelstand creates a significant secondary risk for large German enterprises and multinationals. While a major corporation may have robust defenses, its broader ecosystem of suppliers and contractors often manages sensitive data or maintains privileged network access. To address these systemic gaps, large enterprises must evolve from passive monitoring to a proactive third-party risk management framework, implementing vendor tiering and enforcing multifactor authentication to neutralize the lateral movement favored by modern cyber criminals.

Figure 6: Size of victim organizations found on data leak sites
Targeting Beyond the Assembly Line
Germany's industrial base remains the primary focus for cyber criminals with manufacturing accounting for 23% of all dark web leaks in 2025. However, the German cyber criminal landscape is characterized by its variety, with legal & professional services (14%), construction & engineering (11%), and retail (10%) all targeted.
The most notable shift in the 2025 data is the growth within the legal & professional services sector. This increase is likely intentional: these firms represent high-value targets because they serve as trusted custodians of sensitive client data, including intellectual property, financial strategies, and M&A plans. This allows cyber criminals to extract significant extortion payments beyond their primary victim and gain downstream leverage over an entire client base.

Figure 7: Data leak victims in Germany by industry
Outlook
The data from 2025 reveals that the recent surge in German leaks is not an isolated incident, but a return to the high-pressure levels previously observed in 2022 and 2023. This resurgence reflects a more volatile and linguistically diverse European threat landscape going into 2026. The 92% growth in German leaks, tripling the European average for 2025, proves that non-English-speaking nations remain a primary target for global extortion groups.
The disruption of established brands like LockBit has rebalanced the ecosystem into a crowded field of agile data leak sites, such as SafePay and Qilin. These groups appear to be hitting Germany in lockstep with their global expansion, identifying the Mittelstand and German professional services as high-volume, target-rich environments. As threat actors continue to exploit complex supply chains, smaller organizations will remain critical pivot points for those aiming at the top of the industrial stack.
Recommendations to assist in addressing the threat posed by ransomware are captured in our white paper,Ransomware Protection and Containment Strategies: Practical Guidance for Endpoint Protection, Hardening, and Containment.
Posted in
问问这篇内容
回答仅基于本篇材料Skill 包
领域模板,一键产出结构化笔记论文精读包
把一篇论文 / 技术博客精读成结构化笔记:问题、方法、实验、批判、延伸阅读。
- · TL;DR(1 段)
- · 研究问题与动机
- · 方法概览
投融资雷达包
把一条融资 / 创投新闻整理成投资人视角的雷达卡:交易要点、判断、竞争格局、风险、尽调清单。
- · 交易要点(公司 / 轮次 / 金额 / 投资人 / 估值,材料未明示则写 “未披露”)
- · 投资 thesis(这家公司为什么值得关注)
- · 竞争格局与替代方案