Elastic’s new Custom Threat Intelligence integration

- 标题明确安全领域新能力,但未披露支持的 TI 格式(如 STIX/MISP)
- 未说明如何接入私有威胁源或做规则映射
- 缺乏 API 示例、Kibana 配置截图或检测规则样例
Elastic’s new Custom Threat Intelligence integration | Elastic Blog
New
Forrester Wave Leader, Q2 2025
About usPartnersSupport|ENLogin
[](http://www.elastic.co/)
- Elasticsearch
##### Elasticsearch for...
- ###### Context engineering Get the most relevant context to agents so that they deliver accurate and trusted outcomes
- ###### Vector database Efficiently create, store, and search vector embeddings
- ###### Search powered applications The speed, scale, and flexibility to power modern application experience
- ###### Logs Collect, search, explore, and act on large volumes
- ###### Threat protection Detect, investigate, and remediate cyber threats at scale on real-time data
- ###### Workflows Combine scripted automation with AI reasoning natively in Elasticsearch
##### Elasticsearch components
- ###### Elasticsearch A distributed, RESTful search and analytics engine
- ###### Kibana (Discover, Dashboards) Explore, visualize, and build dashboards using data stored in Elasticsearch
- ###### Elastic Agent Builder Build context-aware agents faster that incorporate all your data and deliver best-in-class relevance.
- ###### AutoOps Easy cluster management with performance recommendations, resource utilization, and cost insights
- ###### Piped query language Simplify workflows and accelerate query response for efficient data processing
- ###### Jina AI search models Jina AI is part of Elastic, bringing best-in-class models for embeddings, rerankers, and URL and doc extraction
##### Deployment options
- ###### Elastic Cloud Serverless Zero operational load so that you can build fasterStart free trial
- ###### Elastic Cloud Hosted Deploy and scale on any cloud in minutes with ultimate controlStart free trial
- ###### Self-managed Elasticsearch Run locally, via Kubernetes, or your own orchestrationDownload
- Solutions
##### Search
- ###### Ecommerce search Improve customers' search experience and drive conversion
- ###### Customer support search Help customers find support information quickly and easily
- ###### Search-driven apps Create engaging apps quickly and easily with Elasticsearch
##### Observability
- ###### Log analytics Centralize and analyze logs using Search AI to detect, investigate, and remediate incidents
- ###### Infrastructure monitoring Monitor, visualize, and analyze the health of your on-premises and cloud infrastructure
- ###### Digital experience monitoring Improve users' experience with real user monitoring (RUM), synthetic testing, and uptime monitoring
- ###### App performance monitoring Monitor, visualize, and analyze the performance and availability of your applications
- ###### AIOps Automatically detect, diagnose, and resolve issues faster with GenAl and ML
- ###### LLM observability Monitor and optimize LLM performance, cost, safety, and reliability
##### Security
- ###### Next-gen SIEM Detect, investigate, and respond to evolving threats with Al-driven security analytics
- ###### Workflows for security Automate alert triage, enrichment, and response natively. No separate SOAR required.
- ###### XDR and endpoint security Secure your endpoints, clouds, and containers with AI-driven insights
- ###### AI for security Automate your triage, investigation, and response workflows with Search AI
- Enterprise
##### Why Elastic?
##### Industry
Financial servicesManufacturingPublic sectorRetailTelecommunicationsView all industries
##### Better together
- ###### Cloud providers Deploy with your favorite cloud marketplace: AWS, Azure, or Google Cloud
- ###### Elastic AI Ecosystem Use Elastic with built-in integrations with leading Al technology providers
- ###### Search AI Partner Program Partner with Elastic so we can find the answers, together
##### Accolades
- ###### AV-Comparatives Elastic earns Endpoint Prevention and Response Certification from AV-Comparatives
- ###### Forrester Wave™ Leader A Leader in The Forrester Wave™: Security Analytics Platforms, Q2 2025
- ###### Gartner Magic Quadrant Leader A Leader in 2025 Gartner® Magic Quadrant™ for Observability Platforms
- ###### IDC MarketScape Leader Leader in IDC MarketScape: Worldwide SIEM for Enterprise 2024
##### Customers

[Search Docusign powers millions of e-signature searches daily with Elasticsearch](http://www.elastic.co/customers/docusign)

[Security UOL slashes incident resolution time by 80% with Elastic Security](http://www.elastic.co/customers/uol)

[Observability Pepsi boosts efficiency and reduces MTTR by 30% with Elastic Observability](http://www.elastic.co/customers/pepsico)
- Resources
##### Launch
- ###### Get started Follow along with beginner guides for each solution
- ###### Demo gallery Play in our hands-on sandbox and watch how-to videos
- ###### Downloads Download Elasticsearch now to get started for free
- ###### Integrations Easily connect Elasticsearch to all the systems that matter
##### Learn
- ###### Docs Learn how to use all of Elastic's products and features
- ###### Elasticsearch Labs Learn how to build with the latest features and abilities
- ###### Elastic Security Labs Understand the threat horizon and see the latest research
- ###### Elastic Observability Labs Explore what's next in monitoring and metric trends
- ###### Blog Read all of the latest company news from Elastic's blog
##### Connect
- ###### Community Join our community of developers on Slack, GitHub, and more
- ###### Events Attend your local meetups, workshops, and Elastic{ON}
- ###### Webinars Check out Elastic webinars and learn directly from our experts
- ###### Discuss Share tips, ask questions, and learn from other developers
##### Get help
- ###### Training Learn Elastic for free and expand your skills with our courses
- ###### Support Get expert advice on your Elasticsearch deployments for fast resolution
- ###### Consulting Drive success with custom support and consulting services
Search

Table of Contents
Table of contents!Image 8: icon-toc-16-blue.svg
- Elastic’s new Custom Threat Intelligence integration
- Key features of the Custom Threat Intelligence integration
- Use case: Understanding a CEL program for custom API ingestion
- Breaking down the CEL program
- CEL initial state
- Bring threat data into your security infrastructure easily
- Close
Elastic’s new Custom Threat Intelligence integration
By
November 19, 2024
!Image 9: 145070_-_Blog_header_image_Switching_from_the_Java_High_Level_(1).jpg.jpg)
- )Share on Twitter
- )Share on LinkedIn
- )Share on Facebook
- )Share by Email
- )Print
In modern cybersecurity, organizations must be prepared to handle a wide variety of threat intelligence data to stay ahead of emerging threats. To support this need, Elastic introduces theCustom Threat Intelligence integration, specifically designed for ingesting indicators of compromise (IoCs) in the STIX 2.1 format. By converting STIX data into the Elastic Common Schema (ECS), this integration makes it simple to bring threat data from diverse sources directly into Elastic for unified analysis and detection workflows.
This integration gives users the flexibility to gather threat intelligence from a range of sources, such as STIX-compliant APIs, TAXII 2.1 servers, and even log files in air-gapped environments.
Key features of the Custom Threat Intelligence integration
The Custom Threat Intelligence integration is built for ingesting and converting STIX data into ECS, allowing users to merge threat intelligence from various external sources into Elastic effortlessly. Below are the integration’s core features:
- **Conversion of STIX indicators to ECS:** The integration is designed to ingest STIX 2.1 format data, converting each indicator into ECS-compatible fields. A default pipeline handles common STIX data mappings automatically, but users can extend functionality by adding custom pipelines for unique STIX indicators or formats as needed.
- **CEL input for API communication:** The integration uses the Common Expression Language (CEL) input to enable flexible communication with STIX APIs. Through CEL programs, the integration can connect to STIX-compliant APIs and retrieve relevant threat intelligence data. This approach allows for highly customizable data ingestion, handling HTTP requests, responses, and data processing in a structured way.
- **Built-in TAXII 2.1 client for simplified data retrieval:** For organizations relying on TAXII servers, the integration includes a built-in CEL program that acts as a TAXII 2.1 client. This client facilitates connections to TAXII 2.x servers, automatically retrieving STIX data with minimal configuration — just the TAXII server URL and any required authentication credentials.
- **Log file support for air-gapped environments:** Recognizing the needs for air-gapped environments, the integration also supports reading STIX-based threat intelligence from log files. This enables organizations in isolated environments to incorporate threat intelligence without requiring direct internet access.
- **Built-in dashboard for visualizing indicators:** The integration comes with a built-in dashboard to visualize ingested threat intelligence indicators, making it easy for users to view and interpret the threat data collected. This dashboard provides an organized view of indicators, helping analysts quickly assess threat intelligence patterns and enhance awareness.
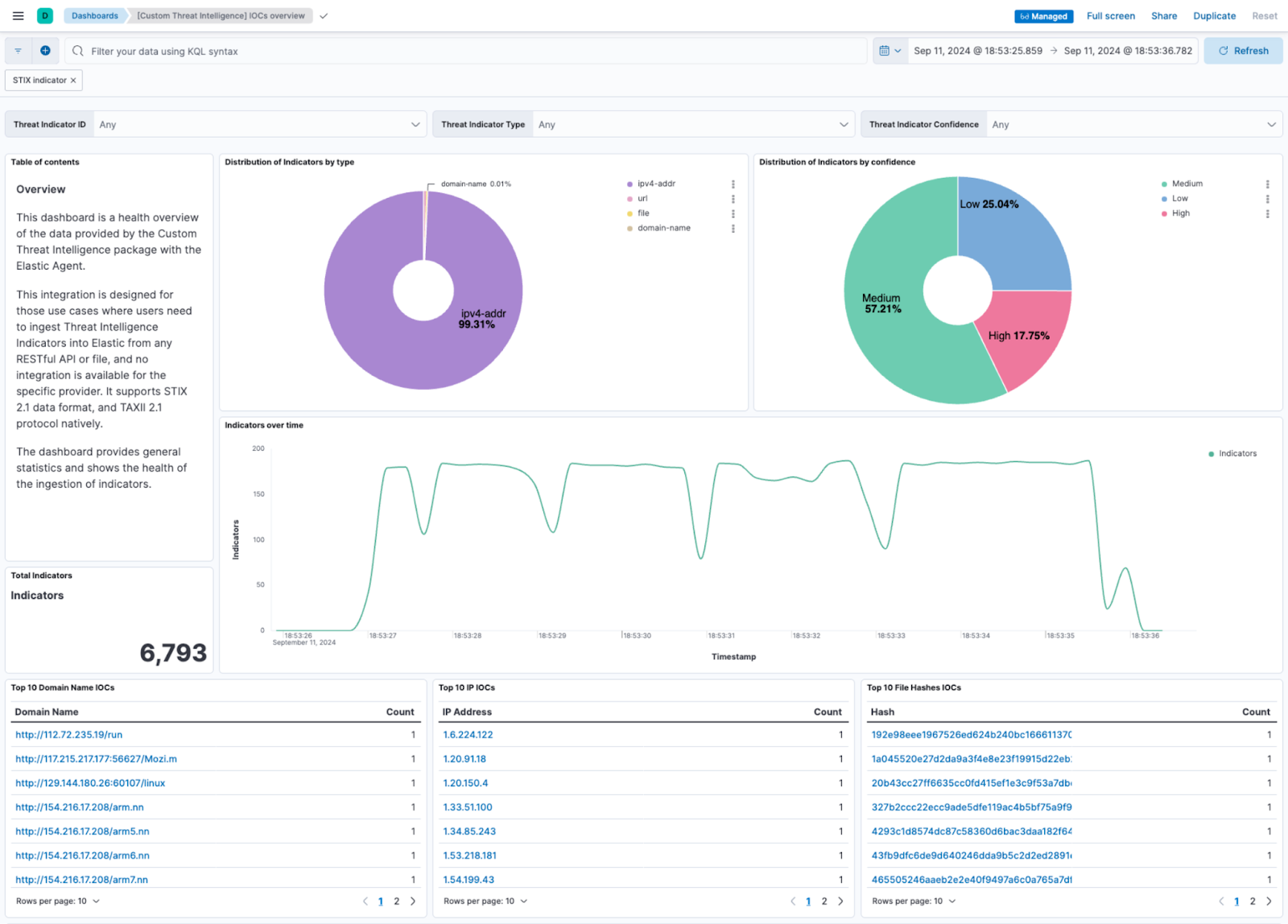
Custom Threat Intelligence dashboard: IoCs overview
Use case: Understanding a CEL program for custom API ingestion
For STIX APIs that do not follow a specific protocol like TAXII, CEL programs allow you to customize the retrieval and processing of threat data. Using CEL, you can define HTTP headers, query parameters, pagination, and payload processing to meet the requirements of the API — ensuring accurate and complete ingestion of threat intelligence.
To show how CEL programs work within the Custom Threat Intelligence integration, let’s break down a sample CEL program. This example shows how a CEL program can be used to retrieve data from a custom STIX API using the GET method and incorporates flexible authentication options based on the presence of an API key or Basic Authentication credentials.
state.with(
request(
"GET",
(has(state.initial_interval) && state.initial_interval != "") ?
(
state.url.trim_right("/") + "?" + {
"start": [(now() - duration(state.initial_interval)).format(time_layout.RFC3339)],
}.format_query()
)
:
state.url
).with(
{
"Header": {
"Authorization": (has(state.api_key) && state.api_key != "") ?
["Bearer " + string(state.api_key)]
: (state.?username.orValue("") != "" && state.?password.orValue("") != "") ?
["Basic " + (state.username + ":" + state.password).base64()]
:
[]
}
}
).do_request().as(resp, (resp.StatusCode == 200) ?
bytes(resp.Body).decode_json().as(body,
{
"events": body.objects.map(e,
{
"message": e.encode_json(),
}
),
"url": state.url,
"api_key": state.?api_key.orValue(""),
"username": state.?username.orValue(""),
"password": state.?password.orValue(""),
}
)
:
{
"events": {
"error": {
"code": string(resp.StatusCode),
"id": string(resp.Status),
"message": "GET:" +
(
(size(resp.Body) != 0) ?
string(resp.Body)
:
string(resp.Status) + " (" + string(resp.StatusCode) + ")"
),
},
}
}
)
)!Image 21Copy to clipboard Copy to clipboard
Breaking down the CEL program
1. **Request construction:** The CEL program constructs an HTTP GET request. If the _initial\_interval_ is set, the request URL appends a query parameter specifying the start time — which is calculated from the current time minus the initial interval. This allows the integration to fetch only recent threat data.
2. **Header setup:** The program dynamically builds the Authorization header to support different types of authentication:
1. If an _api\_key_ is provided, it creates a Bearer token using _Authorization: Bearer <api\_key>_.
2. If the API requires Basic Authentication instead, it checks for _username_ and _password_ fields, encoding them in base64 as required by the Basic <encoded_credentials> format.
3. If neither an API key nor username and password are available, the Authorization header is left empty.
3. **Data processing on successful response:** If the response status is 200 (OK), the program decodes the JSON body of the response and maps each STIX object as an event in Elastic.
4. **Error handling:** If the response status is not 200, the program generates an error event that includes the status code, response status, and any response body content. This error handling provides visibility into any issues with data retrieval.
CEL initial state
Each CEL program requires an initial state definition — which includes key parameters, such as the API URL, authentication tokens, and retrieval intervals. Following the example above, the CEL state for this case could look like this.
url: "https://stix-server.example.com"
username: "<USERNAME>"
password: "<PASSWORD>"
initial_interval: "120h"!Image 22Copy to clipboard Copy to clipboard
When adding a CEL program to the Custom Threat Intelligence integration, ensure the _Enable TAXII 2.1_ toggle is disabled, and paste the CEL program and its initial state into the designated blocks in the integration’s configuration.
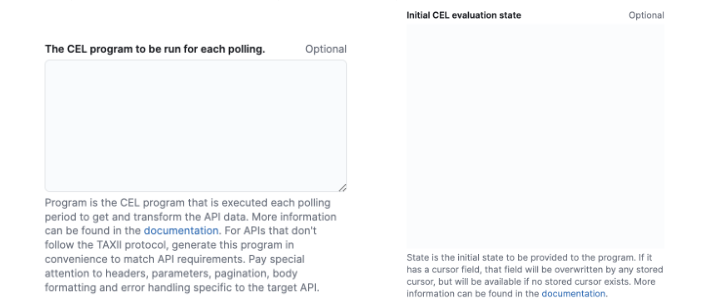
CEL configuration for the integration
This example provides a generic template for using CEL programs to retrieve threat intelligence from STIX APIs. However, users will likely need to adapt the program based on the specific requirements of their STIX server — paying particular attention to query parameters, required headers, and the structure of the response body.
Bring threat data into your security infrastructure easily
Elastic’s Custom Threat Intelligence integration makes it easy to bring threat data into your security infrastructure — giving you more insights to catch and respond to threats faster. With support for STIX 2.1 indicators, connections to TAXII servers, and flexible CEL configurations, this integration is built to fit your specific needs — turning threat intelligence indicators into ECS format so that it works seamlessly across the Elasticsearch Platform.
We’re excited for you totry out these features, explore new use cases, and share your feedback to help us continue evolving threat intelligence capabilities within Elastic.
_The release and timing of any features or functionality described in this post remain at Elastic's sole discretion. Any features or functionality not currently available may not be delivered on time or at all._
Share
- )Share on Twitter
- )Share on LinkedIn
- )Share on Facebook
- )Share by Email
- )Print
Sign up for Elastic Cloud free trial
Spin up a fully loaded deployment on the cloud provider you choose. As the company behind Elasticsearch, we bring our features and support to your Elastic clusters in the cloud.

Follow us
- 
- 
- 
- 
- 
- About us About ElasticLeadershipBlogNewsroom
- Join us CareersCareer portalHow we hire
- Partners Find a partnerPartner loginRequest accessBecome a partner
- Trust & Security LegalTrust centerPrivacyTrade ComplianceEthics & Compliance
- Investor relations Investor resourcesGovernanceFinancialsStock
- Excellence Awards Previous winnersElastic{ON} TourBecome a sponsorAll events
About us
Join us
Partners
Trust & Security
Investor relations
Excellence Awards
© 2026. elasticsearch B.V. All Rights Reserved
This website and all associated content, software, discussion forums, products, and services are intended for professional use only. No consumer use of this website or its content is intended or directed.
Elastic, Elasticsearch, and other related marks are trademarks, logos, or registered trademarks of elasticsearch B.V. in the United States and other countries.
Apache, Apache Lucene, Apache Hadoop, Hadoop, HDFS and the yellow elephant logo are trademarks of the Apache Software Foundation in the United States and/or other countries. All other brand names, product names, or trademarks belong to their respective owners.

问问这篇内容
回答仅基于本篇材料Skill 包
领域模板,一键产出结构化笔记论文精读包
把一篇论文 / 技术博客精读成结构化笔记:问题、方法、实验、批判、延伸阅读。
- · TL;DR(1 段)
- · 研究问题与动机
- · 方法概览
投融资雷达包
把一条融资 / 创投新闻整理成投资人视角的雷达卡:交易要点、判断、竞争格局、风险、尽调清单。
- · 交易要点(公司 / 轮次 / 金额 / 投资人 / 估值,材料未明示则写 “未披露”)
- · 投资 thesis(这家公司为什么值得关注)
- · 竞争格局与替代方案